GPG signature verification
When you’re building software with people from around the world, sometimes it’s important to validate that commits and tags are coming from an identified source. Git supports signing commits and…

When you’re building software with people from around the world, sometimes it’s important to validate that commits and tags are coming from an identified source. Git supports signing commits and tags with GPG, and starting today GitHub will show you when commits and tags are signed.

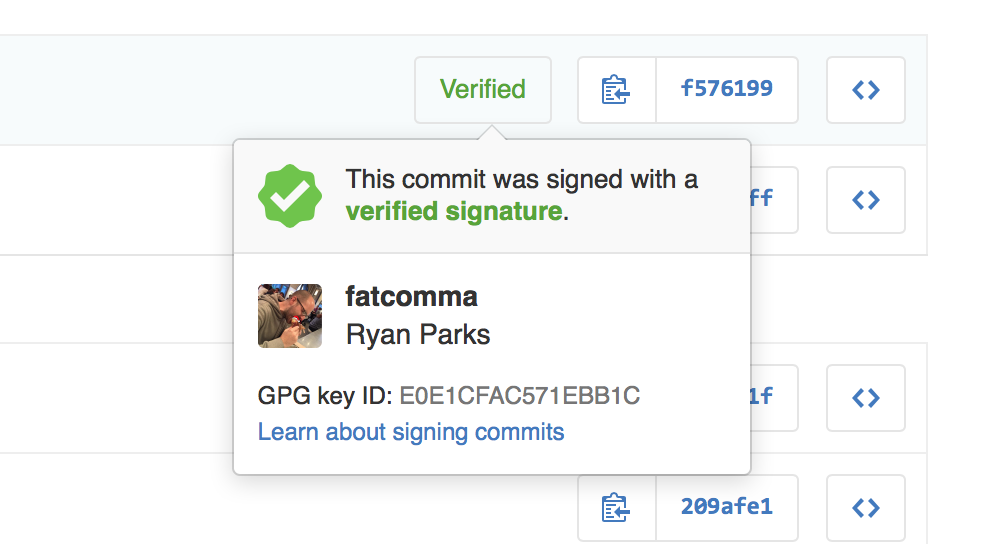
When you view a signed commit or tag, you will see a badge indicating if the signature could be verified using any of the contributor’s GPG keys uploaded to GitHub. You can upload your GPG keys by visiting the keys settings page.
Many open source projects and companies want to be sure that a commit is from a verified source. GPG signature verification on commits and tags makes it easy to see when a commit or tag is signed by a verified key that GitHub knows about.
To learn more about how to generate a GPG key and start signing your work, read our GPG documentation articles.
Written by
Related posts

A maintainer’s guide to vulnerability disclosure: GitHub tools to make it simple
A step-by-step guide for open source maintainers on how to handle vulnerability reports confidently from the start.
Sign in as anyone: Bypassing SAML SSO authentication with parser differentials
Critical authentication bypass vulnerabilities (CVE-2025-25291 + CVE-2025-25292) were discovered in ruby-saml up to version 1.17.0. In this blog post, we’ll shed light on how these vulnerabilities that rely on a parser differential were uncovered.
Full exposure: A practical approach to handling sensitive data leaks
Treating exposures as full and complete can help you respond more effectively to focus on what truly matters: securing systems, protecting sensitive data, and maintaining the trust of stakeholders.